Principal Validation Plugin
Mindbreeze InSpire
Introduction
The Principal Validation Plugin is a session validation plugin that uses a configured caching principal resolution service to retrieve the principals of the user belonging to the current session and validates them against a configured set of accepted principals.
Installation
The plugin is installable via the Mindbreeze InSpire Management Center by uploading the plugin archive in the “Plugins” panel of the “Configuration” section.
Configuration
Configuration requires activating the Principal Validation Plugin for the selected Client Service. As a prerequisite, a configured Caching Principal Resolution Service is needed, running on the same Mindbreeze InSpire Node as the Client Service.
Activating the Plugin
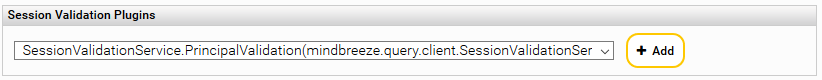
Using the “Advanced Settings” view mode, navigate to the “Session Validation Plugins” section of the Client Service configuration. In the plugin selector dropdown list chose “SessionValidationService.PrincipalValidation” and then click on “Add”:
Configuring the Plugin
Settings
Principal Validation Service Port | The web service port parameter configured for the chosen Caching Principal Resolution Service. Make sure the service is running and the port is correct, otherwise all requests will be marked as invalid. If a user has valid principals all resolved principals by this service will be used as user’s security principals for authorization of search results (matched against result ACL). |
Invalid Session Redirect URL | If configured, in case of an invalid session, a response redirecting to this URL is sent back in the Client Service. |
User Has All Valid Principals | If the option “User Has All Valid Principals” is enabled, all configured valid principals have to be amongst the principals (groups, aliases) resolved by the configured principal resolution service for validating the request. If the option “User Has All Valid Principals” is not enabled then, if any of the configured “Valid Principals” is among the resolved principal set, the request is considered valid. Default is disabled. |
Match Principals Case Insensitive | If checked, the matching between resolved and valid principals is case insensitive. Default is enabled. |
Add Resolved Principals | If this option is enabled, all resolved principals will be used to authorize search hits (ACL). The prerequisite for this is that the session is valid. The decision whether a session is valid depends on the option "User Has All Valid Principals" If this option is not activated, no resolved principals will be used for the authorization of the hits but only for the verification of the session validity. |
Valid Principals | Groups or aliases that are considered valid. |
As soon as the plugin is added and the configured Client Service is restarted with the new settings, the new session validation method is available.
Deployment and Troubleshooting
If configured the Principal Validation Plugin is executed on every request on the Mindbreeze InSpire Client Service where authentication is needed.
If the session is not validated and no “Invalid Session Redirect URL” is configured, an error page is delivered with a HTTP response code 500:
![]()
In the Mindbreeze InSpire Client Service Log the following entry is visible:
2019-03-19 09:04:20.088175 [139896060622592] com.mindbreeze.enterprisesearch.clientservice.session.SessionValidationFilter ERROR: Session is invalidated by SessionValidationService.
If the principal resolution service is not available, and the session validation plugin is active, all requests are invalidated.
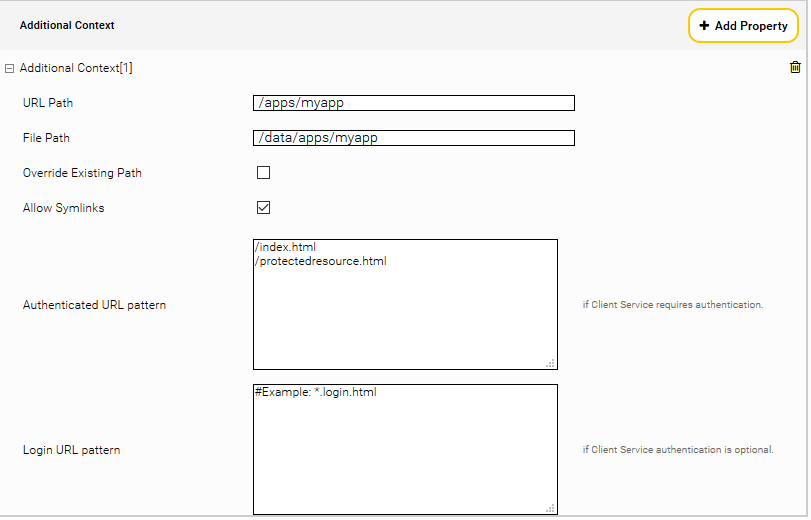
If you are using an error page inside your own web application context as “Invalid Session Redirect URL”, make sure that the page does not require login, otherwise accessing a protected URL results in a redirect loop. You can set this up by configuring the “Authenticated URL Pattern” of your application context in such a way, that the error page URL is not matched.